Protocol Briefing
What's in this lesson: Data classification tiers, data minimization, least privilege, and the 24-hour incident rule.
Why this matters (WIIFM): Applying these rules protects your users, your team, and your own access to production systems.
Experiment: The Urgent Slack
It's Friday, 4:50 PM. You're wrapping up when this notification hits your desktop:
User_Auth_Tokens table to manual-sync. Can you DM it to me ASAP? 5 mins or we crash.
You have the access. The founder is asking. What is your first move?
The SOP: Our Shield
Our Standard Operating Procedure (SOP) is the legal and ethical foundation for how we manage information.
Protect People
Reduce the risk of identity theft, harassment, or financial harm to users whose data we handle.
Protect Compliance
Align with frameworks like GDPR and NIST SP 800-53 by applying structured security controls.
Know Your Data
Not all data is created equal. We classify information into four tiers to determine how it must be handled.
Tier 1: Public
Marketing copy, blogs, public docs. Safe for anyone to see without additional controls.
Tier 2: Internal
Org charts, company memos. Only for active employees and approved contractors.
Tier 3: Confidential
Customer names, emails, business strategy. Access on a documented need-to-know basis.
Tier 4: Restricted
Tokens, hashes, payment and health data. Highest protection; never shared through chat or email.
Knowledge Check: Classification
You find a text file in a shared repo containing session authentication hashes. Which tier is this?
Think of each vault slot as a tier. Which "locker" should hold authentication hashes?
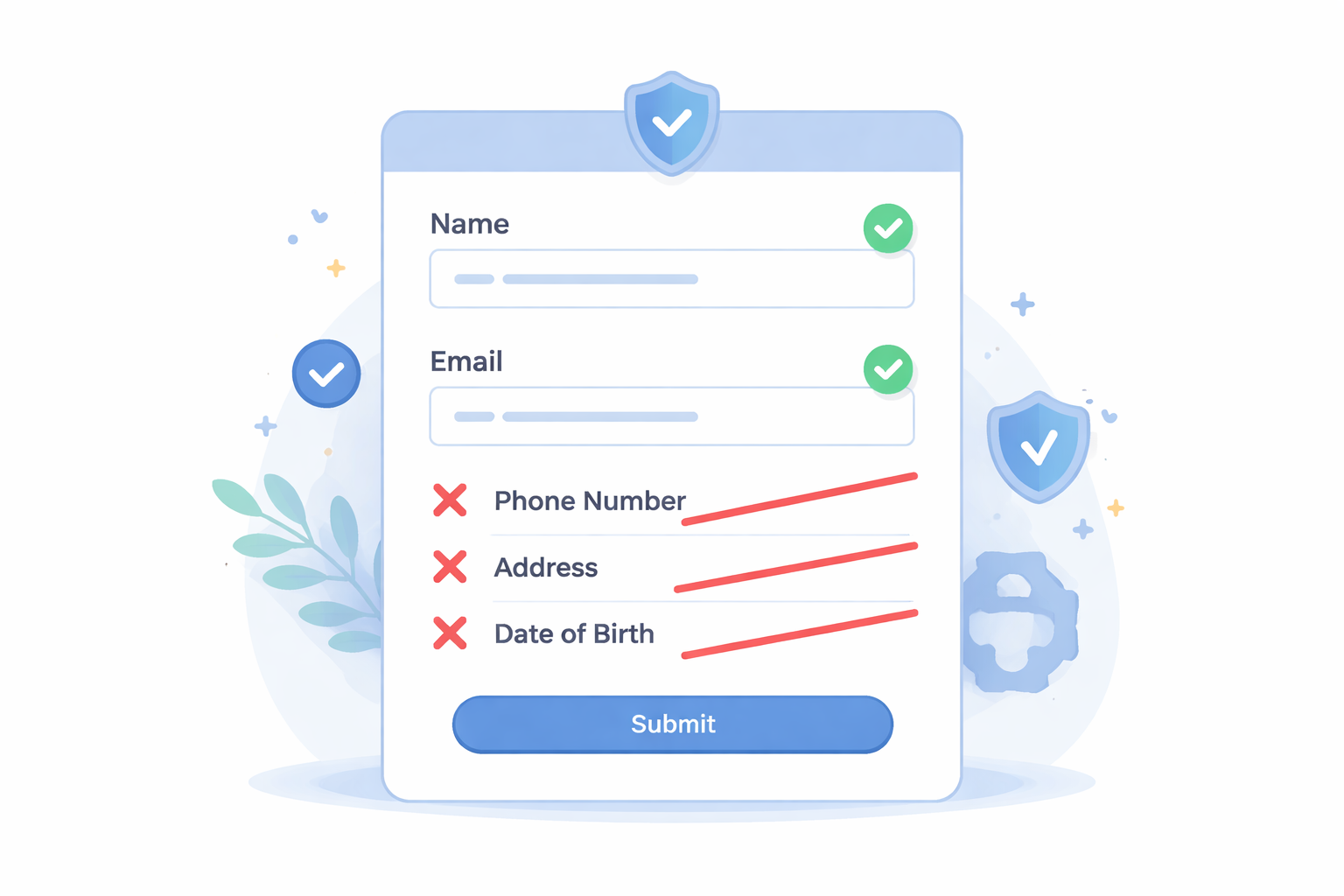
The "Lean" Data Diet
Data minimization means collecting and keeping only what is necessary to perform a specific function.
If a feature only needs a user's postal code to calculate shipping, do not ask for their full address. If you don't store it, you can't lose it in a breach.
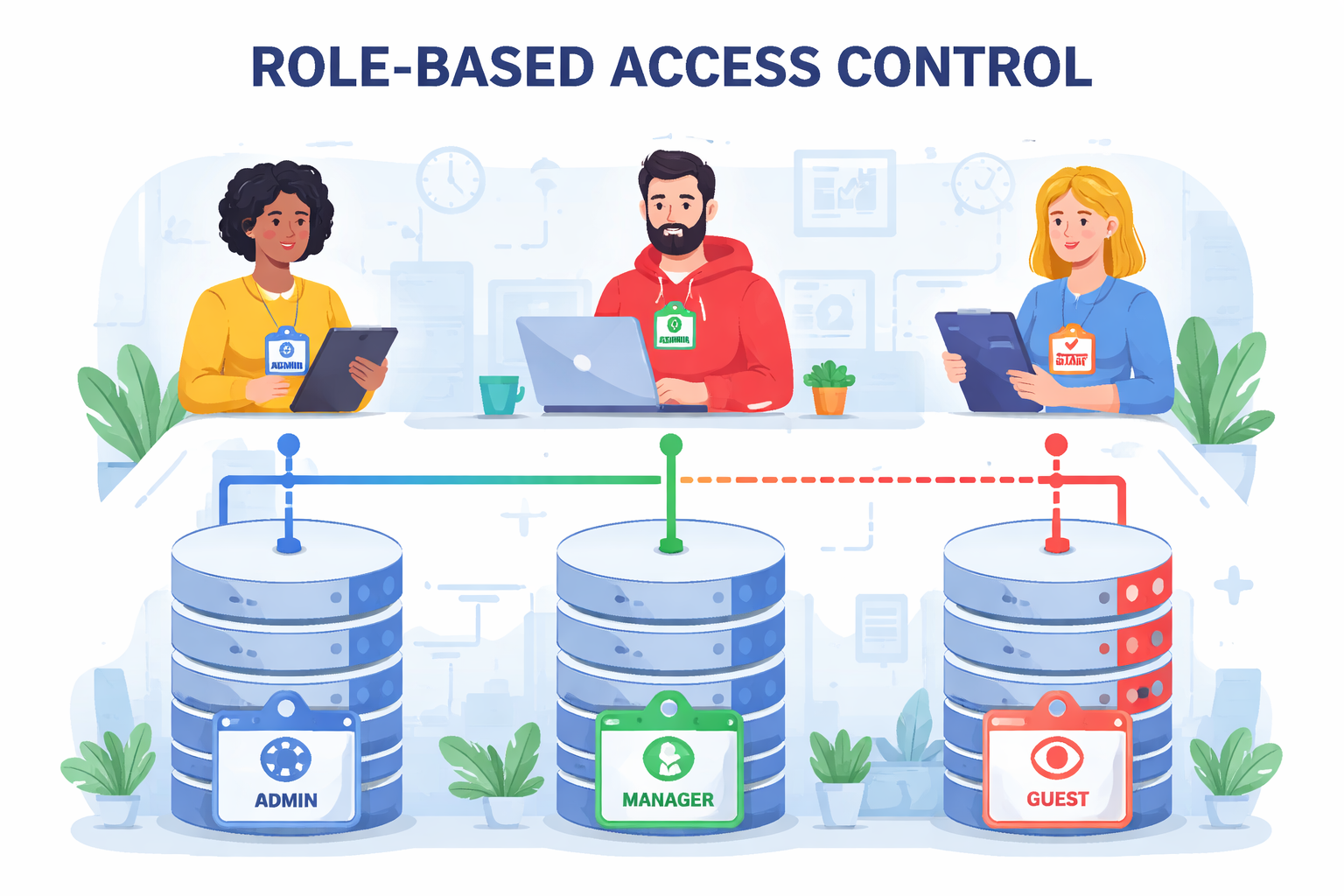
Least Privilege
The principle of least privilege says each person gets only the minimum access needed to do their job.
Just-in-Time
Elevated access is granted temporarily for specific work, then automatically revoked.
MFA Required
All access to Tier 3 and Tier 4 data requires strong multi-factor authentication.
The Data Lifecycle
Information governance covers data from the moment it is created to the moment it is securely destroyed.
- Transit: Encrypted with TLS 1.3 or better.
- At Rest: Encrypted with AES-256 to align with common security controls.
- Retention: Deleted automatically once its business purpose expires.

Knowledge Check: Access
A senior engineer asks to use your login credentials for an hour because their account is locked. What do you do?
This scene shows two users separated by a red block sign. Sharing credentials would knock that barrier down.
The 24-Hour Rule
Mistakes happen. The protocol is simple: if you suspect a breach or mismanaged data, report it within 24 hours.
Silence is the only fireable offense. Contact the Security Officer or post in the #sec-incident channel immediately.
Protocol Summary
1. Classification
Know your tiers. Tier 4 (Restricted) secrets never leave secured systems or channels.
2. Minimization
Only collect and retain data you truly need for a defined purpose.
3. Privilege
Grant the least access necessary, backed by MFA and time-bound approvals.
4. Integrity
Report suspected incidents within 24 hours so the team can contain damage.
Sources: NIST SP 800-53 security and privacy controls, common data protection and incident response best practices.
Ready for the final verification?
Protocol Certification
This assessment verifies your understanding of the Data Privacy SOP. You must achieve 80% to pass.
- 5 situational questions.
- No time limit.
- Certificate awarded upon passing.
